What Is Android Developer Verification? Why Google Is Raising the Bar for Sideloading
Android Developer Verification changes how sideloading works on certified Android devices. This article breaks down the timeline, the advanced flow, the impact on F-Droid, and what independent developers should prepare for next.

Updated: March 20, 2026
Note: This article is based on public materials from the Android Developers Blog, Android Developers documentation, and public discussions on Hacker News. Any explanation of "why Google is doing this now" that is not stated directly by Google should be read as analysis and inference.
If you have seen recent coverage of Android Developer Verification, the two real questions are straightforward: Why is Google raising the bar for Android sideloading, and what does that mean for independent developers, F-Droid, and third-party app stores?
On March 19, 2026, Google published its latest explanation and formally revealed the advanced installation flow for Android Developer Verification. This system does not eliminate sideloading on Android, but it does change the default path ordinary users follow when installing APKs:
- Verified developers keep an installation experience that is close to what users have today
- Students and hobbyists get a free, low-friction limited distribution option
- Developers who do not want identity verification can still distribute APKs, but their users must go through a higher-friction installation path
If you line up the first announcement from August 2025, the early feedback in November 2025, Google's March 4, 2026 post about "choice and openness," and the main reactions from the developer community, the pattern becomes much clearer:
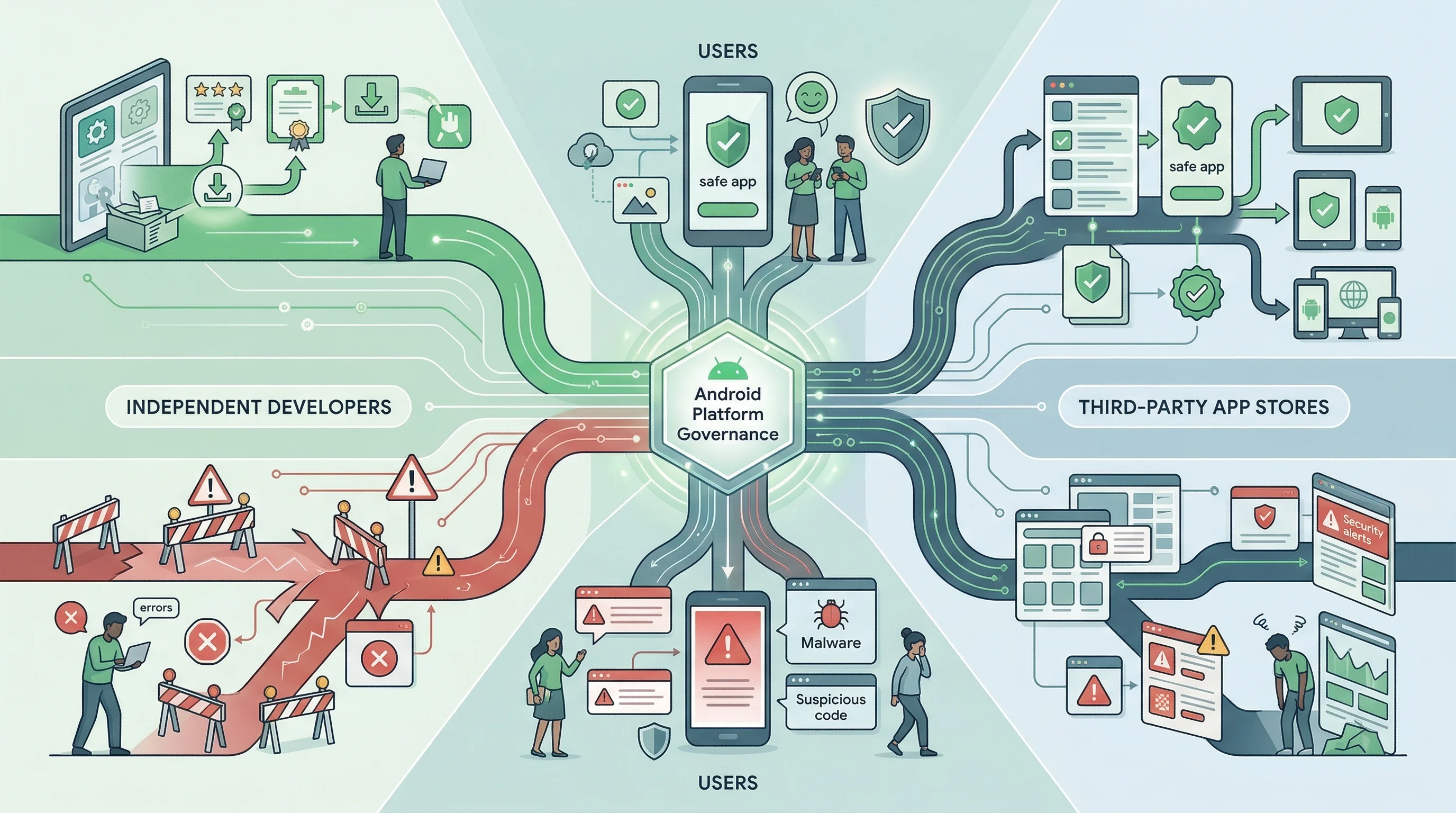
Google is not removing sideloading. It is turning Android's openness from "open by default" into something that is verifiable, attributable, and open in tiers.
That is the part that matters most.
Key takeaways
- Android sideloading is not being removed. Google has repeatedly said sideloading will remain available, and ADB installs are unaffected.
- What is really changing is the default distribution threshold. On certified Android devices, developers who want a smooth install experience for ordinary users will increasingly need to operate in a real-name, registered, and traceable framework.
- Google's public justification is anti-fraud and anti-repeat-abuse enforcement. The company argues that internet-sourced sideloaded malware is far more common than malware on Google Play, and that financial scams increasingly rely on social engineering that pushes victims to install APKs.
- What the community is really worried about is not whether apps can still be installed, but who gets to define the normal installation path. Anonymous open-source projects, the F-Droid ecosystem, and competing third-party stores all become weaker if the default path grows more restrictive.
- From a timeline perspective, this looks like part of a broader restructuring of Android distribution governance. Google is rolling out developer verification while also expanding the Registered App Stores program and billing options, which suggests the goal is not simply to lock distribution down, but to move "openness" into a supervised and certifiable framework.
Android Developer Verification timeline: what changed from 2025 to 2027?
Start with the confirmed timeline.
August 2025: Google first announces developer verification requirements
On August 25, 2025, Google announced that apps installed on certified Android devices would eventually need to be registered by verified developers. Google's justification was direct:
- Google said malware from internet sideloading sources was 50 times more common than malware on Google Play
- Google argued that the core problem is that anonymous developers can repeatedly re-upload malicious APKs
- The policy would first launch in Brazil, Indonesia, Singapore, and Thailand, which Google described as regions more exposed to this type of fraud-driven installation attack
One detail here is crucial and often overlooked: Google explicitly said it is verifying who the developer is, not reviewing APK content itself. In other words, this is not a traditional app review regime. It is a registration regime that ties APK distribution to a real-world identity.
November 2025: Google acknowledges the backlash and starts adjusting the design
By November 2025, Google admitted in its early access post that feedback was concentrated around two groups:
- Students and hobbyists, who worried that identity checks, government IDs, and fees would raise the barrier to learning and experimentation
- Power users and alternative distribution ecosystems, who worried that Android was effectively weakening sideloading
Google then introduced two buffering mechanisms:
- Limited Distribution Account: a free option for students, classrooms, and hobby projects
- Advanced Flow: a higher-friction path for users who still want to install apps from unverified developers
Based on the order of Google's announcements and the design changes that followed in late 2025, the advanced flow looks a lot like an exception path Google added in response to community pressure.
March 2026: Google turns the exception path into a formal public flow
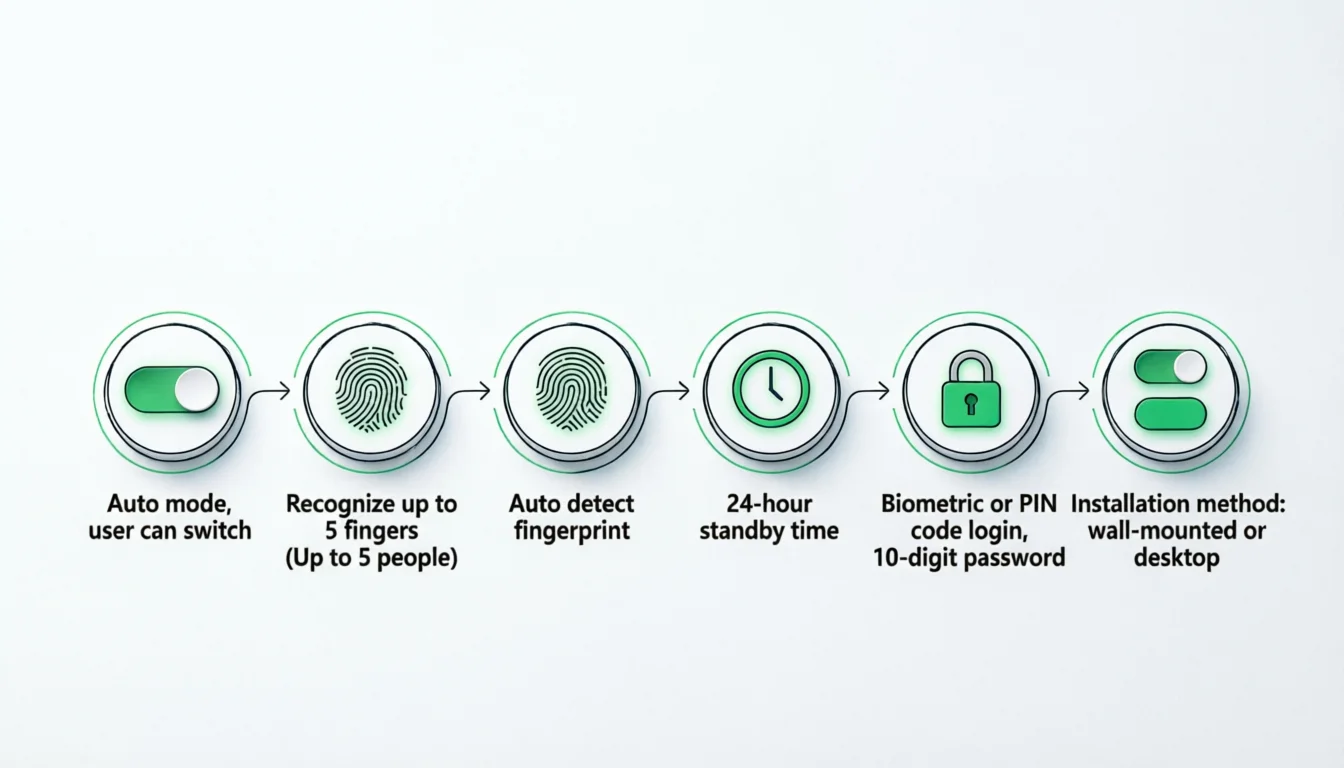
On March 19, 2026, Google formally published how the Advanced Flow works. If a user wants to install an app from an unverified developer, they now need to:
- Enable developer mode
- Confirm they are not being tricked into disabling security protections
- Restart the device and re-authenticate
- Wait through a one-time 24-hour cooling-off period
- Confirm again using biometrics or a PIN
- Then choose whether to allow apps from that unverified developer for 7 days or long term
Google frames this as a coercion-resistant installation design. The idea is that scammers often create intense urgency over the phone and pressure users to dismiss warnings and install an APK immediately. A 24-hour delay, device restart, and re-authentication are meant to interrupt that social-engineering chain.
At the same time, Google also confirmed:
- Limited Distribution Account will launch globally in August 2026
- Advanced Flow will also launch globally in August 2026
- Regional enforcement begins in Brazil, Indonesia, Singapore, and Thailand in September 2026
- Broader global expansion starts in 2027 and beyond
What does Android Developer Verification actually change? How different developer groups are affected
If you only read headlines, it is easy to think Google has "killed sideloading." That is not what the official documentation says.
1. A full distribution path for professional developers
For organizations and professional developers, Google offers the Full Distribution path:
- Identity verification is required
- Apps can be distributed through any channel, including the developer's own website and third-party stores
- For ordinary users, the install experience should remain broadly similar to today
If you already distribute through Google Play Console, much of your verification data can be reused. If you distribute outside Play only, you will use the new Android Developer Console.
2. A limited distribution path for students and hobbyists
Google's biggest concession here is the Limited Distribution account:
- Free
- No government-issued ID required
- Sharing is limited to 20 devices
- Designed mainly for hobby developers, classroom projects, and non-commercial prototypes
At minimum, this shows Google recognizes that not every Android developer should be treated like a commercial publisher.
3. A higher-friction path for unverified developers
If a developer chooses not to verify, distribution is still not completely blocked. Google leaves two exits:
- ADB installs remain available
- Advanced Flow allows end users to install after completing extra on-device steps
This is important because it reveals the real nature of the policy:
Google has not technically erased anonymous distribution. It has downgraded it from a default path to an exception path.
4. Enterprise and managed devices are exceptions
The official FAQ also makes clear that:
- Managed devices under enterprise tooling do not face the same verification requirement
- ADB workflows remain unchanged
That further suggests Google's primary target is not development itself, but large-scale APK distribution to ordinary consumers.
Why is Google raising the bar for Android sideloading now?
This is the part that deserves the closest analysis.
1. The official reason: scams and financial fraud are now central to sideloading policy
Google's public story is consistent: developer verification is meant to combat scams, malware, and repeat abusers.
The logic chain Google presents looks like this:
- Malware from internet sideloading sources is significantly more common than malware from Google Play
- Scam groups often pressure users through phone calls, text messages, and messaging apps
- They trick users into installing APKs described as "bank verification tools," "security updates," or "refund tools"
- Once one malicious APK gets blocked, anonymous actors can quickly come back with a new package name and a new identity
In its November 2025 post, Google even described a specific banking scam pattern in Southeast Asia: scammers claim an account has been compromised and persuade the victim to install a "verification app" that is actually malware capable of intercepting notifications and two-factor codes.
From that angle, Google is no longer treating APK distribution as just a software distribution issue. It is treating it as a financial fraud and social-engineering problem.
That also explains why the design is not a normal "Are you sure?" prompt, but a deliberate 24-hour delay intended to break urgency.
2. The deeper reason: Google wants to extend Play-style identity accountability to the rest of Android
In its 2025 materials, Google explicitly said that after introducing developer verification on Google Play in 2023, it had already seen benefits from stronger identity verification in reducing abusive behavior.
That suggests Android Developer Verification is not an isolated new policy. It is Google extending the governance logic of Play beyond Play itself.
In the past, Play was the tightly governed distribution space, while outside-Play distribution was closer to an "at your own risk" open zone. Now Google seems to be redrawing that boundary:
- Both inside and outside Play move toward developer identity binding
- The difference is no longer "reviewed versus unreviewed," but "smooth by default versus friction by default"
From a platform-governance perspective, this is a familiar pattern: keep nominal openness, but gradually concentrate the smooth path in the hands of entities that can be registered, identified, and audited.
3. Community backlash forced Google to preserve an "openness" narrative
Looking at Google's messaging from November 2025 through March 2026, it is clear the company is responding to strong pushback from developers. That is also why Google published a dedicated March 2026 post about balancing openness, choice, and safety.
The wording of that post suggests Google is responding to three specific criticisms:
- "Are you trying to get rid of sideloading?"
- "Are you forcing every developer into real-name verification?"
- "Are you slowly turning Android into a softer kind of walled garden?"
That is why Google keeps repeating:
- sideloading still exists
- power users can still choose to accept risk
- students and hobbyists still have a free path
In that sense, the March 2026 blog post is fundamentally an explanatory response.
It is not announcing a totally new direction. It is telling the outside world: "We are not closing the door entirely, but the door will no longer be as easy to walk through."
4. My view: this is also part of Google's attempt to reshape Android distribution order
This part should be labeled clearly: what follows is analysis based on Google's timeline, not a cause-and-effect claim stated by Google.
On March 4, 2026, Google published another important post, A new era for choice and openness, which announced:
- broader developer billing choice
- the Registered App Stores program
- smoother installation pathways for third-party stores that meet Google's quality and safety thresholds
If you read the March 4 and March 19 posts together, the framework becomes quite clear:
- Stores and developers that are compliant, registerable, and able to meet Google's thresholds get a better default experience
- Those who do not want to enter that framework still exist in theory, but have to use a higher-friction path
This looks a lot like a new Android openness model:
not "everyone is equally open," but "openness still exists inside a safety and quality framework defined by Google."
For Google, that is easier to control than a world where users are simply expected to assess APK risk on their own. It is also easier to explain to regulators: Android remains open, but within a more accountable governance model.
Main community concerns: F-Droid, third-party stores, and platform control
Hacker News generated a large volume of discussion here, and the emotional pattern was highly consistent. HN is not an official policy source, but it does show what parts of this issue make technical communities uneasy.
1. The main fear is not "can I still install it?" but "has default freedom been downgraded?"
Google's formal answer is: "Yes, you can still install apps. ADB remains available, and the advanced flow can also grant long-term access for unverified apps."
But many people on HN are not satisfied with that answer, because their concern is different:
Once a capability moves from the default path to an exception path, its default availability has already been reduced.
That is why the comment thread repeatedly returns to questions like:
- If today it is a 24-hour wait, what happens tomorrow?
- If long-term allowance exists now, could it be removed later?
- If today it is "just" a scary dialog, will third-party stores be targeted more aggressively later?
None of those are confirmed facts. But they reflect a deeper distrust of Google's platform incentives.
2. F-Droid and open-source distribution are likely to end up in a weaker position
Google's official design does not explicitly target F-Droid, but the structural impact is fairly clear.
For distribution channels like F-Droid, Obtainium, and GitHub Releases, the core question is not whether they are technically blocked. It is whether:
- users are willing to go through a 24-hour wait and extra confirmations
- developers are willing to submit their real identities and documents to Google
- third-party stores are willing to enter Google's Registered App Stores framework
That creates a practical outcome:
unverified developers and distribution channels that stay outside Google's framework may still survive, but their conversion rates and growth potential will likely decline.
For projects that depend on anonymity, non-commercial distribution, or a strong distance from platform gatekeeping, that impact is especially direct.
3. "Is this anti-competitive?" will remain a long-term argument
Another major theme in HN discussions was the connection between this policy and Google's broader antitrust pressure.
This part requires caution: Google does not say developer verification exists for competitive strategy reasons. But from the outside, the controversy is hard to avoid for three reasons:
- Google writes the Android platform rules while also operating Google Play
- The new rules require third-party developers and stores to register identity information with Google to some degree
- Those who do not register are not fully banned, but they are pushed into a worse user-experience path
So this policy will likely remain part of the larger argument between "platform safety" and "platform gatekeeping."
The practical impact on developers, users, and third-party stores
For independent developers and open-source maintainers
If you are a solo developer, especially one who distributes outside Google Play, the issue is no longer one single rule. It is a new stack of release costs:
- identity verification materials
- address or organization proof
- package name and signing-key registration
- the strategic choice of whether you are willing to bind your developer identity more tightly to Google
For commercial developers, these costs are probably just process overhead. For anonymous developers, sensitive-region projects, gray-area software, or non-profit open-source work, they may become structural barriers.
For mainstream users and power users
For mainstream users, Google's logic may work. The kinds of large-scale financial scams Google is worried about often succeed precisely because ordinary users are pressured into dismissing warnings quickly.
For power users, however, the issue is not whether there is still a technical backdoor. It is that:
- setting up a new device becomes more cumbersome
- installing non-Play apps carries a higher cognitive cost
- the long-standing feeling of Android freedom gets weaker
So this policy could achieve two things at once:
- reduce scam success rates
- reduce the psychological attachment advanced users feel toward Android as an open platform
For third-party app stores
Google's March 4 Registered App Stores program is the variable most worth watching next.
If third-party stores choose to join that program, they may get a smoother install flow. If they refuse, they stay in the same higher-friction lane as ordinary sideloaded APKs.
That means the third-party store landscape may split:
- some stores cooperate with Google in exchange for lower installation friction
- some stores insist on autonomy outside Google's framework and accept weaker distribution efficiency
For Google itself
The short-term upside of this policy is obvious:
- it is easier to tell regulators that Android is not "open by neglect"
- it is easier to go after repeat malware distributors
- it is easier to bring developer identity, package names, and signing relationships into one governance system
But the long-term cost is also clear:
- distrust from open-source communities and enthusiast users will keep accumulating
- "Is Android still open?" will increasingly become a question Google has to explain, rather than something that feels self-evident
If you are a developer, what should you do now?
If you are an independent developer, an open-source maintainer, or an operator of a third-party distribution channel, the practical question is no longer whether you like this policy. It is how to reduce release friction before it gets worse.
1. If you distribute APKs to ordinary users
- Evaluate early whether you need the Full Distribution path
- Clean up your existing package names, signing keys, and entity information so later registration does not become chaotic
- Prepare a clearer website, help center, and download instructions so fewer users drop off when they see installation warnings
2. If you are a student, classroom project owner, or hobby developer
- Track the real limits and eligibility rules of Limited Distribution
- Check whether the 20-device cap is enough for testing, demos, and early sharing
- If the project might become commercial later, estimate the migration cost from limited to full distribution early
3. If you rely on F-Droid, GitHub Releases, or your own download page
- Make installation instructions clearer so users are less confused by the advanced flow
- Model the risk of lower installation conversion instead of focusing only on whether installation remains technically possible
- Prepare at least one backup distribution path so you are not overly dependent on a single channel
The most important conclusion to remember
If I had to summarize this entire Android Developer Verification debate in one sentence, it would be this:
Google has not removed Android's openness, but it is turning openness from a default right into a conditional, attributable, and tiered capability.
That is why Google can honestly say "sideloading is here to stay," while the developer community can still feel that Android is getting narrower. Both sides are observing the same reality from different levels:
- Technically, the door is still there
- Institutionally, the threshold at that door is clearly higher
And the most important question for the future is not whether Android will completely block sideloading in September 2026. It is this:
Will Google keep concentrating the "smooth install" path in the hands of developers and stores that accept its identity and quality framework?
If the answer is yes, Android openness will not vanish overnight. But it will look more and more like a form of openness that must be applied for, registered, and continuously maintained.
FAQ
Will Android sideloading be removed completely?
As of March 20, 2026, the official answer is no. Google explicitly says sideloading will remain available, ADB installs are still supported, and unverified apps can still be installed through the Advanced Flow.
When does Android Developer Verification start being enforced?
The official timeline is:
- March 2026: registration opens to all developers
- August 2026: Advanced Flow and Limited Distribution launch globally
- September 2026: regional enforcement begins in Brazil, Indonesia, Singapore, and Thailand
- 2027 and later: gradual global rollout
Will F-Droid still work?
Yes, but whether the experience feels the same as today depends on whether a given app completes verification and whether users are willing to go through the Advanced Flow. Under the official mechanism, F-Droid is not technically blocked, but unverified apps in its ecosystem will face more installation friction.
Do students and hobbyists need to submit a government ID?
No. Google has confirmed a free Limited Distribution account for students, classroom projects, and hobby developers. It supports sharing apps on up to 20 devices and does not require a government-issued ID.
Is this Google strengthening its control over Android distribution?
Google would not describe it that way. Its public justification is anti-fraud enforcement and stronger developer accountability. But from a platform-governance perspective, smoother installation paths will clearly become more concentrated among developers and stores willing to enter Google's framework, so "more control" is a reasonable outside interpretation.
Related reading
- If you want to understand how platforms redraw risk boundaries in the name of security, read Is OpenClaw Safe? Officially Documented Risks and Hardening Advice
- If you are more interested in what new platform friction means for open ecosystems, read AI Slop Is DDoSing Open Source Maintainers
Sources
- Android developer verification: Balancing openness and choice with safety - Android Developers Blog (2026-03-19)
- Android developer verification - Android Developers Guides (updated 2026-03-19)
- Frequently asked questions - Android developer verification
- Register for limited distribution on Android devices
- Android developer verification - Android Developers overview
- For developers on the new Android Developer Console
- A new layer of security for certified Android devices - Android Developers Blog (2025-08-25)
- Android developer verification: Early access starts now as we continue to build with your feedback - Android Developers Blog (2025-11-12)
- Let's talk security: Answering your top questions about Android developer verification - Android Developers Blog (2025-09-30)
- A new era for choice and openness - Android Developers Blog (2026-03-04)
- Global Scams on the Rise: Over Half of Adults Worldwide Report Scam Encounters - GASA (2025-10-07)
- Hacker News discussion: Android developer verification: Balancing openness and choice with safety
Source Notice
This article is published by merchmindai.net. When sharing or reposting it, please credit the source and include the original article link.
Original article:https://merchmindai.net/blog/en/post/android-developer-verification-sideloading-analysis